While browsing on the net I ran across something every interesting called the PS4 playground by CTurtE. It’s a collection of PS4 tools and experiments using the WebKit exploit. Now this is for firmware 1.76 only at the moment.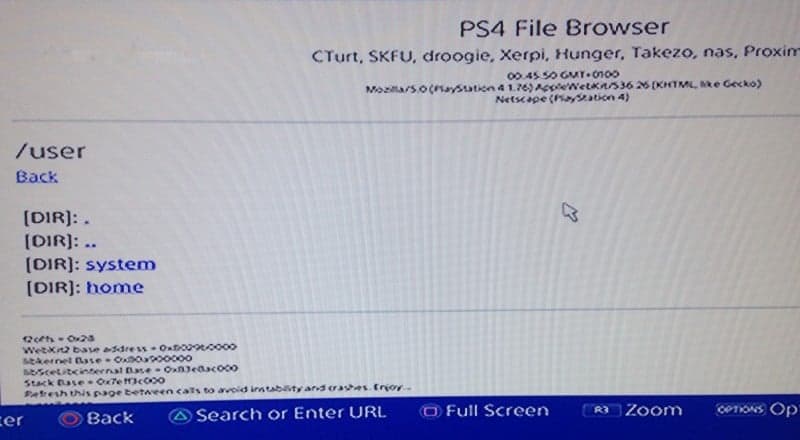 If any of you remember around the time of the PS4 update 2.00, Skfu told everyone to stay on FW 1.76 if you were interested in any hacks for the PS4. Well today we see that the web exploit did bear fruit, so if you are still on FW 1.76 give it a try and let us know how it goes in the comments below.
If any of you remember around the time of the PS4 update 2.00, Skfu told everyone to stay on FW 1.76 if you were interested in any hacks for the PS4. Well today we see that the web exploit did bear fruit, so if you are still on FW 1.76 give it a try and let us know how it goes in the comments below.
Setup
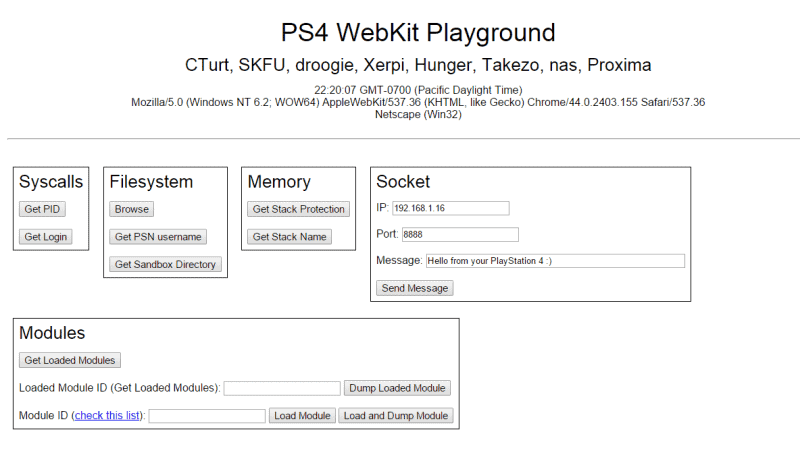
A live demo can be tried here, without module dumping, seen in the picture below.
You should clone the repo and upload it your own server to have module dumping capabilities:
git clone git://github.com/CTurt/PS4-playground.git
You can also download a zip of the latest source here.
Usage
Although this is this primarily a framework to help write and execute ROP chains, PS4-playground comes with several experiments for you to try.
After executing a test, you should either refresh the page, or close and reopen the browser entirely; running multiple experiments sequentially is not reliable.
Syscalls
Get PID – Get process ID
Get Login – Get login name and leak a kernel pointer
Modules
Get Loaded Modules – Get a list of currently loaded modules
Dump Loaded Module – Dump a currently loaded module (use Get Loaded Modules to see all available)
Load Module – Load an additional module from this list
Load and Dump Module – Load an additional module and then dump it (see all available here)
Once you have dumped a module, you will need to run dir2bin.py to combine all chunks into a single binary.
Filesystem
Browse – File Browser
Get PSN username – Read your PSN username from account.dat
Get Sandbox Directory – Get the name of the current sandbox directory (10 random characters which change each reboot)
Memory
Get Stack Protection – Get stack base, size, and protection
Get Stack Name – Get stack base, size, and name
Socket
Send Message – Send a TCP message to the specified IP and port
Special thanks to SKFU, droogie, Xerpi, Hunger, Takezo, nas and Proxima for their help on it.
Download: PS4-playground