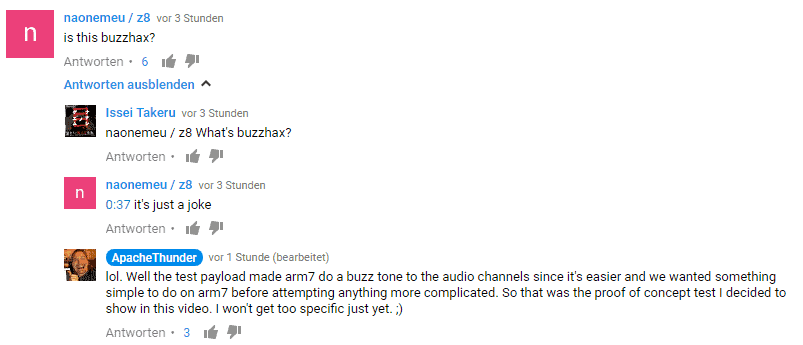
Since the 3DS Security is pretty much full blown with nothing left to it, Devs seem to have picked interest in the still not really hacked DSi. Since the last public exploits have been patched since Firmware 1.4.2 and except for a bit of homebrew nothing really has been achieved, they are now working again on hacking this great little Device. The Beginning of all this may have been Developer Robz8 creating SRLoader for the DSi which allows booting .nds Roms from the SDcard. Since this is only able to be done with the old 1.4.2 hacks, he hinted that new DSiWare Hax are in the works. Meanwhile, another type of hax seems to also be in the works for the DSi which seems to be based on NTRCardHax. Here’s the Video by Apache Thunder. (Better turn down the volume at the end, there is a loud buzzing sound ;))
Credits for this Hack go to NoCash, Gericom, Normmatt, StuckPixel and Apache Thunder for making this happen.
After watching the video a few times crying, since the DSi will finally get the love from hackers it never really got, and some guessing on GBATemp we now know that this Hack uses DSi Firmware 1.4.0 since that Firmware came without a proper Flashcard whitelist. Sure, Finding a DSi on that Firmware today should be pretty much impossible but with the DSiWare Exploit hinted at by Robz8 we should be able to simply downgrade our DSi to Firmware 1.4.0. As seen in the video he seems to insert a Cartridge into the DSi which causes it to make the annoying buzzing sound. According to Apache Thunder that’s a test Payload for the Arm7 Processor. We can also see Zelda 4 Swords there but in this case, this should be completely irrelevant.
I’m really really curious what the revived DSi Scene will be able to do with our old DSi’s and what we can do with it someday when the Hacks are finished. I really hope for something like Arm9LoaderHax or even better, Boot9Hax. Just finding a way to install DSiWare to the SDCard and still being able to launch it would also be great though 🙂
If you want to keep an eye on the guesses that are made for this exploit and maybe some more information soon™ you should check out this thread.
Source: Apache Thunder