While I was combing though github this neat little program PortDog caught my attention. PortDog is a detector aimed to detect port scanning. So what the hell is port scanning?
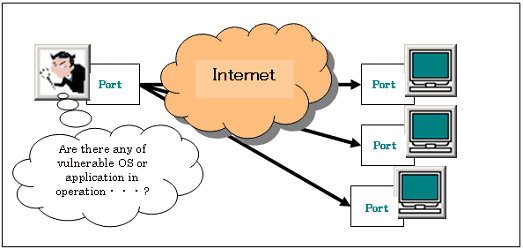
Port Scanning, is one of the most popular techniques used to discover services that can be exploited to break into systems. All systems that are connected to a LAN or the Internet via a modem run services that listen to well-known and not so well-known ports. By port scanning, anyone can find the following information about the targeted systems: what services are running, what users own those services, whether anonymous logins are supported, and whether certain network services require authentication.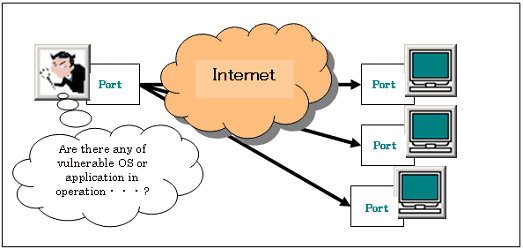
Port scanning is accomplished by sending a message to each port, one at a time. The kind of response received indicates whether the port is used and can be probed for further weaknesses. Port scanners are important to network security technicians because they can reveal possible security vulnerabilities on the targeted system. Just as port scans can be ran against your systems, port scans can be detected and the amount of information about open services can be limited utilizing the proper tools. Every publicly available system has ports that are open and available for use. The object is to limit the exposure of open ports to authorized users and to deny access to the closed ports.
That is why PortDog caught my attention.
“It’s a network anomaly detector aimed to detect port scanning techniques. It is entirely written in python and has easy-to-use interface. They have tested on Ubuntu 15, please note it does not work on Windows OS due to suffering from capturing RAW packets. They are working on a new write up for this script to work on both platforms. In future, they are thinking about adding firewall options that could block malicious attempts. It is using Raw packets for analysis. For this reason, make sure that you run this script from a “privileged session”.
Usage:
sudo python portdog.py -t time_for_sniff_in_minutes
For example, if you want to detect for 5 minutes use:
sudo python portdog.py -t 5
For infinite detection use:
sudo python portdog.py -t 0
If you want to get the list of scanned ports , press CTRL+C to get port list at runtime (If scan was happened).
Download: PortDog