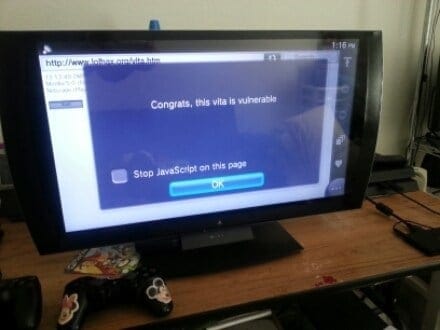
It’s been about half a year since when Davee released his Proof of Concept for the first WebKit Exploit working on the Vita. It is known that this exploit was independently found by different parties and even working on the PS4. But then Sony found out about it aswell and patched said exploit for both systems with the firmware updates 3.30 (Vita) and 2.00 (PS4).
Well as it seems the exact same thing just happened again, as the last Vita firmware update 3.50 (PS4 2.50?) patched yet another WebKit Exploit.
As far as we know this exploit (CVE-2014-1303) was found by Liang Chen of Keen Team and they decided to release it to the public. Read more about it here:
eu-14-Chen-WebKit-Everywhere-Secure-Or-Not.PDF
eu-14-Chen-WebKit-Everywhere-Secure-Or-Not-WP.pdf
Liang_CanSecWest2015.pdf
Now speaking for the PlayStation Scene the next step has already been done as well! What I’m speaking about is the implementation of this exploit to Hykem‘s Vitasploit (Exploitation Framework) which is a great piece of software that allows exploring the native part of the Vita’s software. As for the public it ‘only’ worked for 2.02, 2.12, 3.00, 3.01, 3.15 and 3.18! And of course we need to see if this exploit can be ported over to the PS4, or is already.. ?!!
But what does all this mean for me as a normal Vita user? Well if you haven’t took your time to play with Vitasploit already, I’d strongly recommend to do so!
For everyone else, here’s a little introduction: Opening up the Package Installer and other Apps with support_uri calls, dumping system files for further investigations and test system functions like touch, controls audio and gyroscope.
And this is by the way how the native Pong Sample from February was achieved:
So on the one hand it’s nice to have yet another webkit exploit working, but on the other one it’s sad that Sony patched it and we’re limited to investigate on lower Firmwares again.. 😉
Download the updated vitasploit: vitasploit-33x.zip (release and port via xyz)
For finalisation Hykem already stated to implememt it to his repository and vitasploit, which will from now on have two separate exploit methods!
Catch me on twitter: @freakler94